If you are running a multi-account TikTok matrix, you have likely encountered the dreaded "zero views" glitch. You post high-quality content, use premium proxies, and pace your actions perfectly, yet the algorithm completely restricts your reach.
More often than not, the culprit is not your content strategy—it is your hardware infrastructure.
In 2026, TikTok's anti-fraud algorithm runs deep, kernel-level diagnostics on the device you are using. If you are trying to scale your operations using desktop Android emulators or cheap cloud virtual machines (VMs), you are setting off massive red flags. To fix the TikTok zero views glitch, growth teams are migrating to True ARM Cloud Phones.
This guide explains how TikTok detects emulation, compares the core differences between x86 Virtual Machines and native ARM architecture, and helps you select the best cloud phone infrastructure for your social media matrix.
Why TikTok Bans Virtual Machines (x86 Emulators)
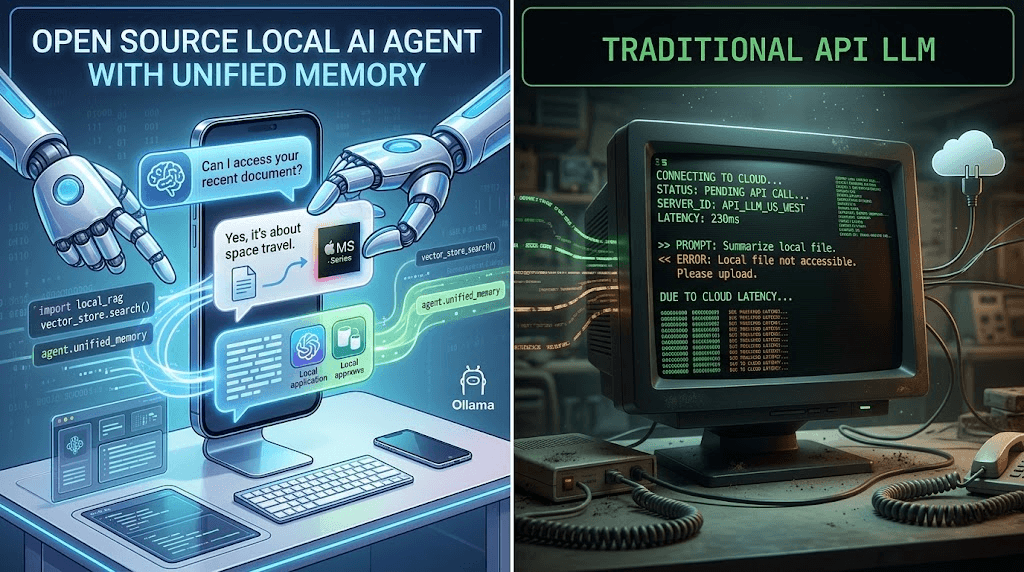
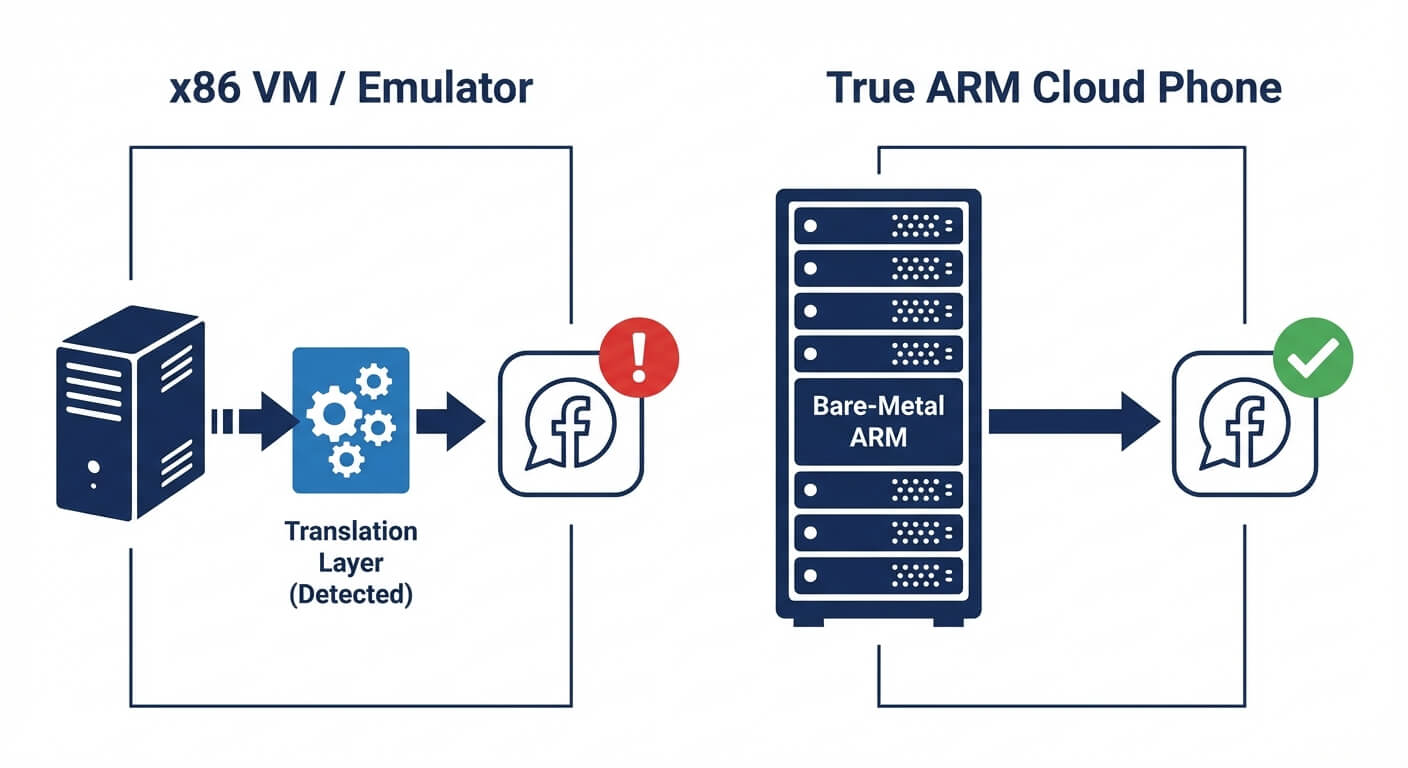
To understand why traditional cloud emulators fail, we have to look at how modern computer processors are built. There are two primary hardware architectures in the world today: x86 and ARM.
Most desktop computers, laptops, and traditional cloud servers (like AWS or Google Cloud) run on x86 processors (built by Intel or AMD). However, nearly all mobile devices (smartphones and tablets) run on ARM processors (like Apple Silicon or Qualcomm Snapdragon).
Because the TikTok application was built exclusively for mobile devices, its code is compiled to run on ARM architecture.
The Emulation Trap: If you use a Virtual Machine emulator (such as BlueStacks, Nox, or a cheap x86-based cloud Android server) to run TikTok, the x86 processor cannot read the ARM code natively. It has to use a software "translation layer" (like Houdini) to convert the ARM instructions into x86 instructions in real-time.
TikTok's security algorithm detects this translation layer instantly. When the app realizes it is being run on an x86 server pretending to be a mobile phone, it immediately flags the session as high-risk, resulting in shadowbans and locked accounts.
What is an ARM Cloud Phone? (The Native Solution)
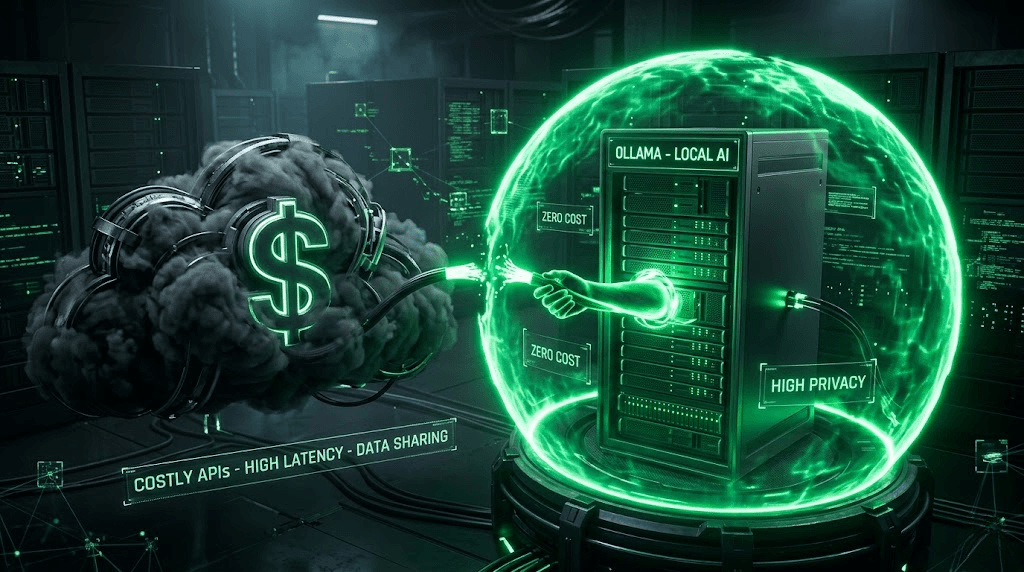
The only way to completely bypass emulator detection is to remove the translation layer entirely. This is where ARM Cloud Phones come into play.
A true ARM Cloud Phone is not a virtual machine running on a standard server. Instead, it is a server rack physically filled with hundreds of actual mobile micro-processors (ARM chips).
When you log into an enterprise ARM Cloud Phone (such as the infrastructure provided by Jumei), the Android operating system and the TikTok app run natively on bare-metal mobile hardware.
No translation layer: The app executes exactly as it would on a physical Samsung or Google Pixel device.
Authentic Telemetry: Native ARM boards provide real hardware telemetry, including authentic CPU clock speeds, battery temperature readings, and genuine GPU rendering data, which x86 VMs struggle to spoof accurately.
Infrastructure Comparison: ARM vs. VMs vs. Physical Phones
When deciding how to manage multiple TikTok accounts safely, you must weigh the operational costs against the ban risk.
Here is an objective comparison of the three primary ways to host a TikTok matrix:
Infrastructure Type | Core Architecture | Execution Method | TikTok Detection Risk | Scalability | Best For |
|---|---|---|---|---|---|
Desktop Emulators / VMs | x86 (Intel/AMD) | Software Translation (Emulation) | Extremely High (Near 100%) | High | Basic web scraping, offline mobile gaming |
Physical Phone Farm | ARM | Native Mobile Device | Low (If networked correctly) | Very Low (High manual labor) | Localized, small-scale operations |
True ARM Cloud Phones | ARM | Native Bare-Metal Server | Low (Matches organic hardware) | Extremely High | Large-scale B2B outreach, TikTok/IG matrices |
The Operational Reality: While building a physical wall of 100 smartphones is technically safe from hardware detection, managing the batteries, screens, physical SIM cards, and individual VPN routers becomes an administrative nightmare. This operational friction is why serious growth teams are rapidly pivoting toward building a scalable cloud farm using remote ARM nodes.
3 Rules for Selecting the Best Cloud Phone for TikTok
Not all cloud phones are created equal. Many budget providers advertise "cloud phones" but actually sell nested x86 VMs. If you want to protect your digital assets, verify these three features before purchasing.
Rule 1: Verify Native ARM64 Architecture
Ask the provider directly if their servers run on ARM64 architecture or if they use x86 virtualization. If they use x86, walk away. TikTok's algorithm will eventually catch the hypervisor signature, and your entire account network will be compromised.
Rule 2: Strict Network Isolation Support
A pristine ARM hardware profile is useless if your IP address is blacklisted. The best cloud phone providers allow you to bind a dedicated, static residential proxy to each individual ARM node. You must ensure your hardware isolation is matched by strict network compartmentalization.
Rule 3: Support for Visual AI Automation
Once you have 50 or 100 secure cloud phones, you need a way to operate them without hiring an army of manual clickers. Top-tier cloud control systems (like Jumei) integrate natively with Visual AI Agents. These agents read the cloud phone's screen and simulate human-like thumb swipes and organic typing delays, replacing easily detectable code-based scripts.
How to Deploy a Safe TikTok Matrix on ARM Infrastructure
Transitioning to ARM architecture is the first step. However, you must still adhere to strict platform compliance rules to ensure account survival. Follow this deployment framework.
Step 1: Provision and Isolate
Spin up your required number of ARM Cloud Phone nodes. Assign a unique static residential IP to each node. Crucial: Maintain a strict 1:1:1 ratio. One TikTok Account = One ARM Node = One IP Address. Never cross-contaminate.
Step 2: The Soft Hardware Transition
If you are migrating existing, aged accounts from a physical phone to a cloud phone, the platform will detect the hardware change. Treat this as a new login event.
Do not post videos or send automated DMs for the first 48 hours.
Allow the algorithmic trust score to stabilize on the new ARM hardware footprint.
Step 3: Paced Algorithmic Warm-Up
Use your AI Agent to perform "dummy" actions that mimic a normal user. Have the agent open the TikTok app, scroll the "For You" page for 15 minutes, watch videos to completion, and drop 1 or 2 neutral likes. Do this daily for 3 to 5 days to build a compliant behavioral history.

Step 4: Scale with Variation
Once the hardware environment is trusted, you can begin your matrix operations. However, avoid spamming identical content. Ensure your workflow alters video metadata, uses AI to generate unique text overlays, and spins captions so the TikTok algorithm views every post from your ARM nodes as original, native content.
People Also Ask (FAQ)
Can TikTok detect BlueStacks or Nox? Yes. BlueStacks, Nox, and LDPlayer are x86 Android emulators running on your desktop computer. TikTok easily detects the x86-to-ARM translation layer and the presence of hypervisor files. Using these for a TikTok matrix will almost certainly result in zero views or account suspensions.
Are ARM cloud phones legal to use? Yes. An ARM cloud phone is simply remote computer hardware. It is completely legal to rent remote hardware. However, you must ensure that your actions on the platform (like the frequency of your automated DMs or posting) comply with TikTok's Terms of Service regarding spam and artificial engagement.
Do I still need proxies if I use a cloud phone? Absolutely. Hardware security and network security are two different layers. The ARM cloud phone provides a pristine hardware footprint, but if 50 cloud phones connect to TikTok using the same datacenter IP address from the cloud provider, TikTok will ban all 50 accounts for IP clustering. You must route each cloud phone through a unique residential proxy.
What is the difference between Jumei and standard cloud phone providers? Many retail cloud phone providers cater to mobile gamers looking to run games 24/7. Enterprise platforms like Jumei are built specifically for B2B digital marketing. They prioritize strict environmental isolation, bare-metal ARM architecture, and seamless integration with Visual AI automation workflows designed to bypass social media anti-bot systems.
Final Thoughts: Stop Fighting the Algorithm
The era of tricking social media platforms with cheap desktop emulators and spoofed browser fingerprints is permanently over. Algorithms are now hardware-aware.
The secret to a successful TikTok matrix is not finding a "magic script," but rather aligning your infrastructure with what the platform expects to see. By migrating your operations to native ARM Cloud Phones, you remove the translation layer, neutralize emulator detection, and provide the platform with the authentic mobile telemetry it demands.
Test your infrastructure first. Provision a small batch of ARM nodes, secure your IPs, and observe the baseline views of your content. Once you confirm your hardware foundation is invisible to the algorithm, you can safely scale your matrix to dominate your market.